
Malware diversified into File Infectors that attached to executables and Macro Viruses that targeted productivity software like Microsoft Word.
Contemporary threats use AI-driven techniques to evade detection. Fileless malware operates in a system's memory to avoid leaving traces on disks, while state-sponsored attacks target critical infrastructure for espionage. Modern Defensive Strategies Malware Evolution
Initial programs like Creeper (1971) were experimental and self-replicating. The first PC virus, Brain (1986) , targeted boot sectors, and the Morris Worm (1988) became the first major Internet-wide incident. Malware diversified into File Infectors that attached to
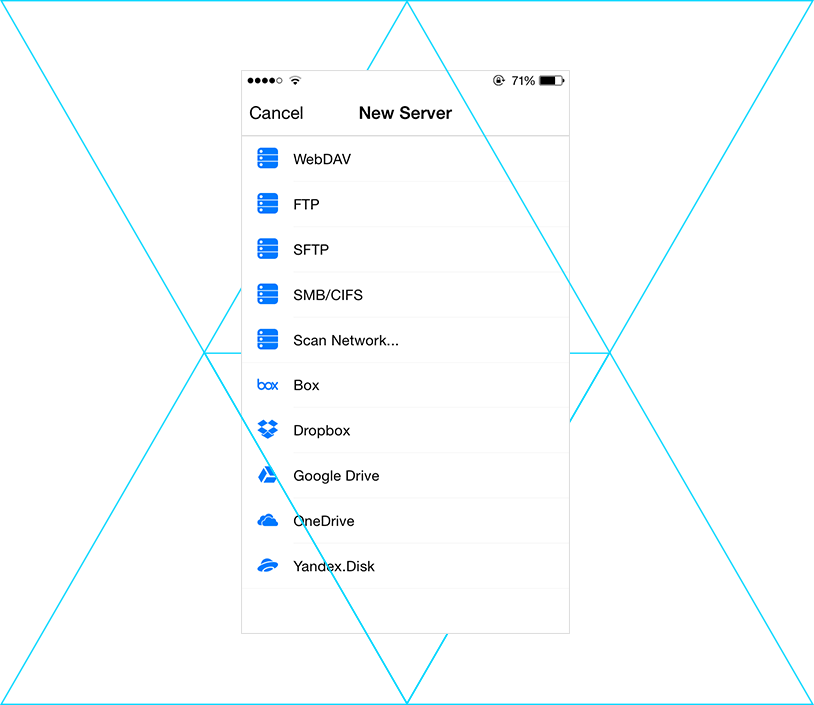
To counter this rapid evolution, cybersecurity researchers use several advanced techniques: targeted boot sectors
Criminal intent became the primary driver. Ransomware emerged as a dominant threat, encrypting user data for profit. Sophisticated Advanced Persistent Threats (APTs) and Ransomware-as-a-Service (RaaS) models also appeared.
