nthLink is built on technologies that have defeated even the strictest internet censorship systems. It automatically:
Unlike many VPNs that store often-obsolete address lists in their apps, nthLink’s mobile app can connect to the Internet even when it has been a long time since you have used it.
The nthLink app calculates fresh server addresses based on where you are and the device you are using, enabling you to connect even in locations where many of its addresses are being blocked. It keeps trying until it finds a secure connection for you.
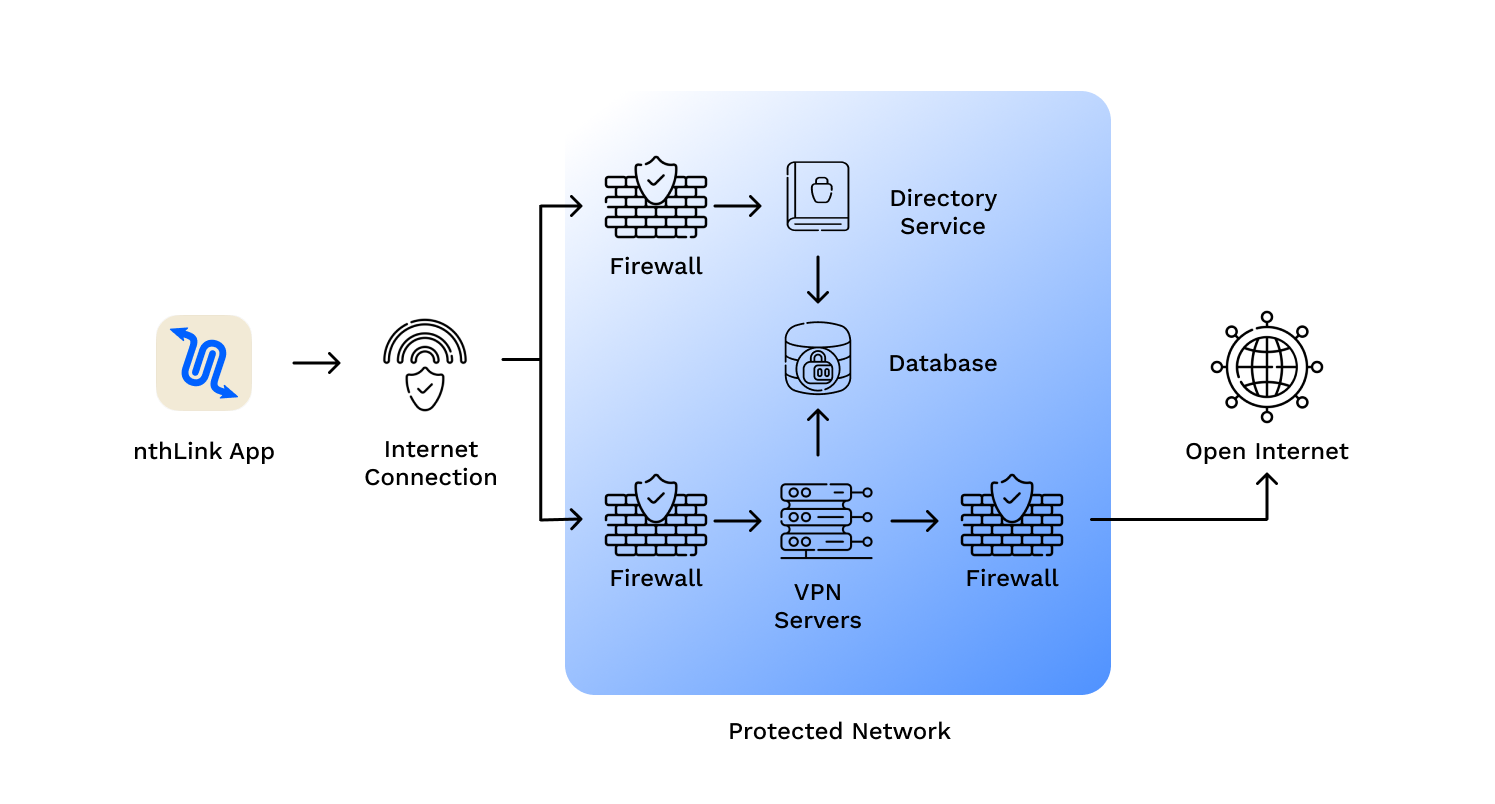
Just install and tap the button and you’re online – inside a reliable and secure network.
We do not track your activities and use best data minimization practices for our server infrastructure.
nthLink uses the strongest available encryption standards so your Internet traffic cannot be inspected.
: Often, these strings correspond to massive libraries of academic texts, high-definition media, or legacy software that is no longer available through official channels. The Risks of the Unknown
: Users must rely on the reputation of the source or the community that posted the link. In this environment, "U9155EIQY9" isn't just a file name; it's a test of digital literacy and caution. Conclusion Download U9155EIQY9 part3 rar
: RAR files can be used to deliver "compressed bombs" or executable malware hidden within the archive. : Often, these strings correspond to massive libraries
Downloading a file with a non-descriptive, alphanumeric name like "U9155EIQY9" carries significant digital risk. Conclusion : RAR files can be used to
While "Download U9155EIQY9 part3 rar" appears to be a mundane technical command, it actually serves as a window into the complex world of online data management. It highlights the necessity of multipart compression for large-scale data transfer and the persistent, often risky, human effort to preserve and share information in the digital age.
The file extension indicates a compressed archive created with WinRAR. When a file is too large for standard upload limits or unstable connections, it is split into multiple "parts" (e.g., part1, part2, part3).